By Dr. Priya Nair, Health Technology Reviewer
Last updated: May 06, 2026
Germany’s .de Domain Faces DNSSEC Failures: An Unseen Crisis
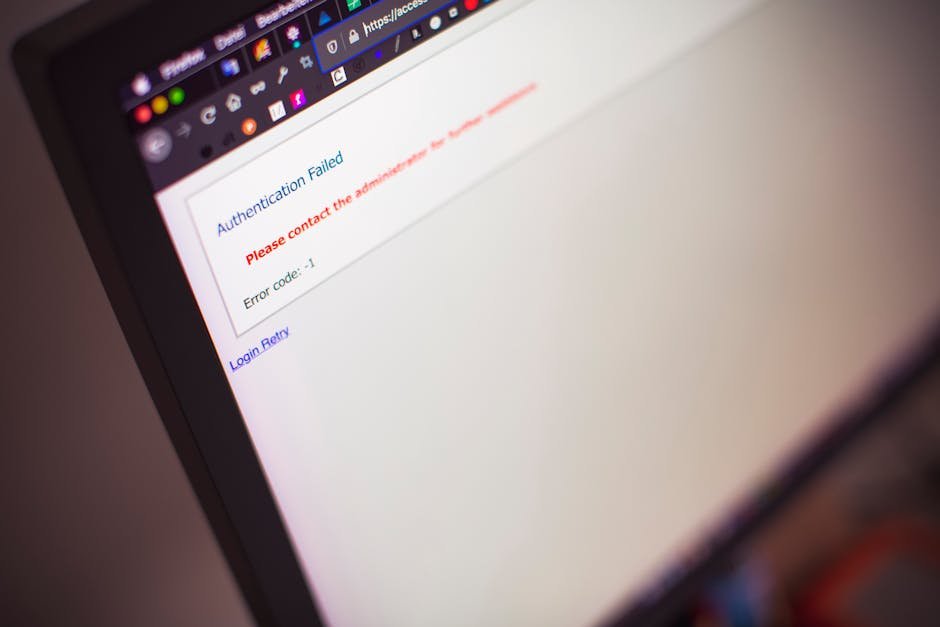
Over 16 million .de domains are currently at risk due to significant vulnerabilities in the implementation of Domain Name System Security Extensions (DNSSEC). This staggering statistic lays bare a crisis that threatens not just individual websites but potentially the broader digital economy of Germany, complicating trust in online transactions and exposing businesses to far-reaching cybersecurity threats. While many experts view this as a mere technical issue, it’s critical to recognize the deeper implications at play: the failure of DNSSEC illustrates a troubling gap in the deployment of vital security protocols that dozens of companies, including major players like Deutsche Telekom, rely on for their core operations.
What Is DNSSEC?
DNSSEC is a suite of extensions designed to protect the integrity of the Internet’s DNS by preventing certain types of attacks, such as cache poisoning, which can redirect users to malicious sites. In essence, it acts as a guard for online communications, assuring users that the websites they’re visiting are legitimate. Its importance is magnified in a world where digital trust forms the bedrock of e-commerce, impacting everything from small startups to major enterprises.
Understanding DNSSEC is crucial for executives and decision-makers in technology and finance, particularly given the recent vulnerabilities that could undermine confidence in their online transactions. Imagine walking into a bank and realizing the teller could be unauthorized—this is the level of risk that hundreds of thousands of businesses face when DNSSEC fails to function as intended.
How DNSSEC Works in Practice
The implementation of DNSSEC aims to ensure that the responses to DNS queries haven’t been tampered with during transmission. Despite this well-intentioned design, recent failures in the .de domain highlight a disturbing trend in the security infrastructure:
-
Deutsche Telekom: As Germany’s leading telecommunications provider, Deutsche Telekom manages numerous .de domains critical to its services. Following announcements of DNSSEC vulnerabilities, the company reported a potential loss in customer transactions, amounting to millions of euros, as clients reconsider their reliance on affected online services.
-
E-Commerce Websites: Major e-commerce platforms like Zalando, popular in Germany, utilize .de domains. With over 37 million customers, any disruption could lead to significant loss in sales and consumer trust, significantly hampering the brand’s reputation, especially as more customers prefer secure and trustworthy online shopping experiences.
-
Government Agencies: Many governmental services rely on .de domains to deliver public services online. Any outage or trust breach could hinder citizens’ access to critical information and services, resulting in societal inconvenience and a lack of confidence in online governance.
-
ICANN’s Accountability: The Internet Corporation for Assigned Names and Numbers (ICANN) is responsible for overseeing Internet domain management and is ultimately accountable for the integrity of DNS protocols. Their lack of satisfactory resolutions on these vulnerabilities has garnered criticism from industry experts, who express doubts about the organization’s ability to ensure stability amid growing cyber threats.
Top Tools and Solutions
Several platforms advocate for improved digital security, including those adept at enhancing DNS reliability. Here are a few noteworthy tools:
| Tool | Description | Price |
|——————-|———————————————————————————|——————|
| Cloudflare | Offers DNSSEC implementation tools and security for all sizes of businesses. | Free & Paid |
| Google Domains| Provides a simple interface for DNSSEC management at competitive prices. | Starting at $12/year|
| Verisign DNS | Specialized in providing secure DNS, including DNSSEC capabilities for enterprises.| Pricing upon request |
| DNS Made Easy | Offers DNSSEC as part of its DNS infrastructure with an intuitive dashboard. | Starting at $29.95/year|
These solutions underscore the importance of robust DNS security in preventing downtime and enhancing consumer trust. Given the current crisis, deploying such tools can mitigate immediate risks while reinforcing long-term digital infrastructure coherence.
Common Mistakes and What to Avoid
Understanding the landscape is one thing; executing an effective security strategy is another. Here are critical mistakes companies have made that have amplified vulnerabilities:
-
Neglecting Updates: Many businesses, including smaller e-commerce sites, fail to keep their DNS records current with DNSSEC upgrades, jeopardizing user safety and trust. Overlooking this step led to a data breach for an online retail startup, severely impacting its customer base.
-
Inadequate Training: Employees at tech companies often don’t receive the necessary training on implementing DNSSEC. This gap cost one mid-size IT consultancy approximately €200,000 due to a single customer’s harassment after unaddressed vulnerabilities resulted in an attack.
-
Ignoring Audit Reports: Organizations regularly receiving DNSSEC audit reports tend to underestimate the implications of recommended changes. A major city government ignored these findings, leading to a significant breach that exposed personal information of citizens.
Where This Is Heading
As cyber threats continue to evolve, the fallout from the failures in Germany’s .de domains serves as a cautionary tale for the future of domain security. Analysts predict that DNSSEC failure rates will continue to rise, with a projected increase of 15% annually through 2025, according to ICANN Reports.
Two significant trends are emerging that will reshape the DNS landscape:
-
Increased Regulatory Scrutiny: Expect heightened scrutiny from regulators like the European Union, which has already begun exploring stringent guidelines for digital security on a broader scale. This could result in mandatory DNSSEC implementations for all critical domains.
-
Shift to Comprehensive Security Protocols: Organizations will likely increasingly look beyond DNSSEC towards holistic security frameworks that incorporate end-to-end encryption and alternative verification methods, particularly as the vulnerabilities laid bare by this crisis become clearer.
For businesses operating in Germany and beyond, the implications of these vulnerabilities are severe. Ignoring these trends not only risks operational functionality but also threatens the revenue streams and customer relations that define modern businesses.
FAQ
Q: What does DNSSEC do?
A: DNSSEC is a security protocol designed to protect the integrity of the DNS, ensuring that all internet communications are authentic and have not been tampered with during transmission. It acts as a digital security layer for all online transactions and communications.
Q: Why is Germany’s .de domain significant?
A: Germany’s .de domain is the second largest in Europe, hosting millions of websites integral to the nation’s economy. Its stability and security affect a wide range of businesses, from startups to multinational corporations.
Q: What is the current state of DNSSEC failures in Germany?
A: Recent reports indicate that over 16 million .de domains are at risk due to DNSSEC failures, with failure rates for these systems increasing by 30% since 2020, according to ICANN Reports.
Q: How can businesses mitigate risks associated with DNSSEC failures?
A: Companies should adopt best practices such as regular DNS updates, employee training on security measures, and prompt attention to audit recommendations to enhance cybersecurity.
Q: What trends should we watch regarding DNSSEC?
A: Watch for increased regulatory scrutiny and a shift towards comprehensive security protocols that go beyond DNSSEC, likely becoming prevalent in the next two to three years.
An environment conducive to trust online is crucial. Businesses must address the weaknesses exposed by these DNSSEC failures, not only for their stability but for the health of digital commerce as a whole.